
Plaintiff Lisa Gill filed a class action lawsuit in the U.S. District Court for the Northern District of California on April 1, 2026, claiming a data breach affected. Mercor.io Corp., a fast-growing artificial intelligence hiring startup. The cyberattack allegedly exposed the sensitive personal data of more than 40,000 people.
The suit claims Mercor failed to maintain basic cybersecurity protections, leaving current and former contract employees and customers vulnerable to identity theft and fraud. Gill seeks damages on behalf of herself and a nationwide class of anyone whose personal information the breach compromised.
San-Francisco based Mercor.io runs an AI-powered hiring platform that connects specialized domain experts, including scientists, doctors and lawyers, with technology companies that need help training AI models and chatbots. The company's clients include major AI developers OpenAI and Anthropic.
LiteLLM supply chain attack
The cyberattack at the center of the lawsuit stems from what security professionals call a "supply chain attack." In this type of attack, hackers compromise a third-party software tool that other companies rely on rather than targeting a victim directly. This approach allegedly allows criminals to reach many companies at once through a single point of entry.
According to the complaint, the attack entered Mercor's systems through LiteLLM, a widely used open-source software tool.
SecurityWeek reported the LiteLLM incident occurred on March 27, 2026. Attackers reportedly used stolen developer credentials to publish two malicious versions of the LiteLLM software package. Thousands of companies allegedly downloaded the software before LiteLLM detected the attack.
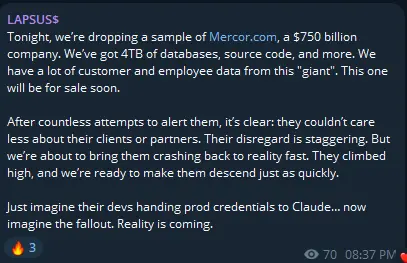
After the attack became public, a hacking group the complaint identifies as "Lapsus" claimed responsibility for the breach. The group, also known as "Lapsus$," is known for targeting high-profile technology companies through extortion.
According to the complaint, the group claimed to have exfiltrated four terabytes of data from Mercor's systems, which it listed for auction on the dark web.
Mercor publicly confirmed the security incident, stating it was "one of thousands" of companies the breach affected. The company said its security team moved quickly to contain the breach and that it brought in third-party forensics experts to support a thorough investigation.
Allegations of cybersecurity failures
The complaint argues Mercor could have prevented the breach and that Mercor's cybersecurity practices fell well below industry standards.
It claims Mercor did not implement multifactor authentication, a security system that requires users to confirm their identity in more than one way before accessing a system.
The lawsuit further alleges that Mercor failed to encrypt sensitive data during storage and transmission. Encryption is a process that scrambles data so that only authorized parties can read it.
Additionally, the suit claims Mercor did not limit which employees or systems could access sensitive personal information, did not monitor its systems for unusual or suspicious activity and did not rotate passwords regularly to reduce the risk of attackers exploiting old or stolen credentials.
Extensive relief sought
The proposed class covers all U.S. residents whose personal information unauthorized parties accessed or acquired during the breach.
The personally identifiable information at issue may include full names, Social Security numbers and other sensitive data belonging to current and former Mercor contract employees and customers.
Gill alleges she lost significant time dealing with the consequences of the data breach and faces an elevated risk of identity theft.
More broadly, the lawsuit claims invasion of privacy, theft of personal information, reduced value of personal data, lost time and a rise in unwanted spam communications. It also alleges loss of the benefit of the bargain, a legal concept referring to the idea that users gave their data to Mercor with a reasonable expectation of security that the company reportedly did not deliver.
The lawsuit asks the court to award compensatory damages to cover actual losses, as well as consequential, statutory, nominal and punitive damages.
Beyond financial compensation, the suit seeks extensive injunctive relief, asking the court to order Mercor to overhaul its data security systems, build out a comprehensive information security program, provide credit monitoring services to affected individuals, submit to annual security audits and hire independent, third-party security auditors.
As of the time of publishing, plaintiffs filed at least three other class action lawsuits in federal court relating to the Mercor data beach.
.png)







.webp)
.webp)
.webp)

.webp)
.webp)
.webp)
.webp)






.svg)